LONG READ
CybSafe’s 2023 security awareness predictions
Introduction
Another year, another series of year-end round-ups and predictions from industry voices. The truth is, what 2023 has in store for us is anyone’s guess—but we’re here to make an educated one.
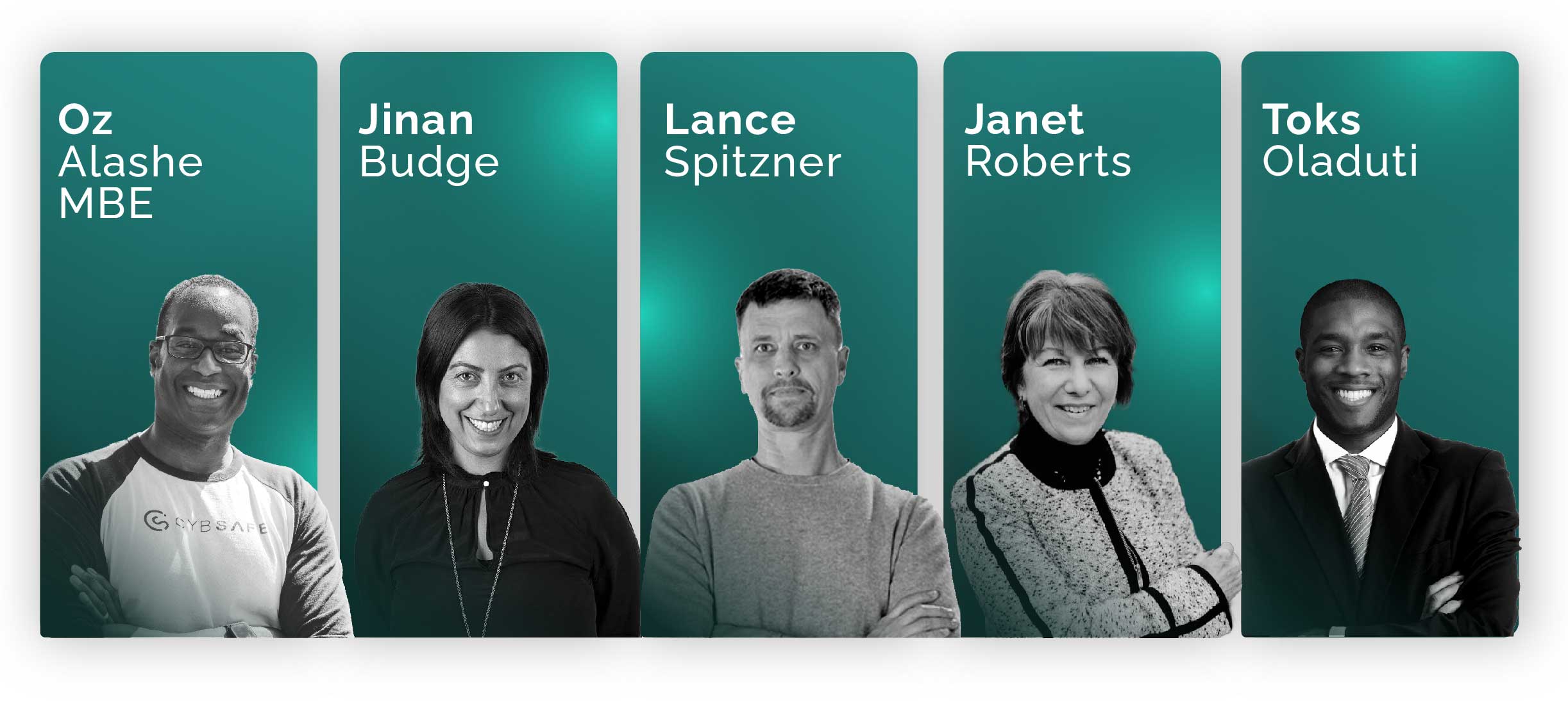
To round out our analysis, we’ve put together a powerhouse of a panel for our free, 2023 predictions webinar. The webinar will be hosted by CybSafe CEO & Founder, Oz Alashe. He’ll be speaking with Jinan Budge, Principal Analyst at Forrester; Lance Spitzner, Director at SANS Security Awareness; and Janet Roberts, Global Head of Security Education and Awareness at Zurich Insurance. This is not one you want to miss.
Alright, back to the write-up! We’ve broken our predictions down into five categories:
Cybercrime and the threat landscape
Governance and the Analysts
Cyber insurance
Security behaviors and human cyber risk
Jobs and the cybersecurity skills gap
Now, sit back, relax, and prepare to be prepared for 2023 (see what we did there?).
1. Cybercrime and the threat landscape
The never-ending game of cat and mouse will continue. Criminals will find new ways to attack. And security professionals will find new ways to help prevent them. That’s why we’re starting our guidance with what guides us—the threat landscape.
Oh look, if it isn’t our archenemy, ransomware
Ransomware has dominated the threat landscape—and the headlines—for the past five years. And it’s not going anywhere. At least not in 2023.
But that doesn’t mean any organization that got through 2022 without a ransomware attack is in the clear. In cybersecurity, doing the same thing over and over doesn’t guarantee the same result (i.e., security). Especially when criminals keep switching things up.
In the last few months alone, criminals realized they don’t need to steal or sell data. That just takes too much time and effort. Simply threatening to delete the data produces the same result—getting organizations to pay up.
Criminals infiltrate an organization’s network, and demand a pay out. If they don’t get one, they delete the data and move on to the next victim. This “wiper malware” has been on the rise, and we’ll likely be seeing a lot more of it in the coming year.
Don’t be held to ransom…by the headlines!
Of course, where there’s malware, there’s media. So, gear up for some sensationalist reporting. You know, the kind that makes organizations consider paying a ransom in a bid to keep a low profile, and stay out of the papers.
To be clear, ransomware, wiperware, and any other type of malware are preventable. It starts with some basic cyber hygiene: network segmentation, backups, regular patching, and vulnerability assessments.
That’s just the technical stuff. A key part of any organization’s cybersecurity defense is its people. When people feel empowered to identify and report security incidents—they do.
But that kind of culture change doesn’t come from security awareness training. It’s the product of management taking time to understand security behaviors—why people do what they do, or don’t do what they’re supposed to—and how to influence them.
MFA is really going to blow up
Not in a good way. According to data from “Oh, Behave! The Annual Cybersecurity Attitudes and Behaviors Report 2022”,
43% of participants had never heard of multi-factor authentication (MFA). The report is available, for free, here.
So, while MFA adoption isn’t expected to shoot up in 2023, MFA bombing is.
An MFA bombing, or ‘MFA fatigue attack’ is when a criminal spams a target with multiple verification requests until the target eventually gives in and approves one. It’s a little like being in a family group chat and not being able to switch off the notifications.
In other words, they are designed to wear people out. And that’s just what the Uber hacker did.
Using a contractor’s compromised VPN credentials, the attacker repeatedly tried to login, spamming the contractor with an MFA notification each time. After an hour or so, the attacker—posing as an Uber IT tech—reached out to the contractor, and persuaded them to accept the latest MFA request. And just like that, the attacker gained access to Uber’s critical systems.
This is a classic example of organizations using a security mechanism (MFA) to reduce compromise, but attackers finding ways to circumvent it.
The way forward? Configuring MFA systems to limit the number of attempts someone has to verify their identity before the account is locked down to allow for additional validation. It’s the same method we’ve been using to guard against password guessing for years.
At the same time, people should be educated to spot, stop, and report these attacks.
2. Governance and the Analysts
Generally, security professionals can consider themselves lucky if they get to see more than a couple of major policy changes before they hit retirement. If you’re looking for an excuse to pop some Champagne, here’s what you need to keep an eye on:
Resilience and privacy are coming in hot
While cybersecurity law will likely continue to focus on the “technology” aspect of the People, Process, and Technology framework, we’re seeing ‘cyber resilience’ take center stage.
Cyber resilience is an organization’s ability to cope with unforeseen incidents, both malicious and accidental, that can cause harm, destruction, or loss of ability to serve customers.
Be it in financial services, insurance, technology companies, law firms, manufacturing, retail, or healthcare—the concept of cyber resilience will become more relevant.
Privacy laws will also continue to develop, albeit slowly. The aim will be establishing comprehensive data protection frameworks to address “security relative to risk”. While we realize nothing is likely to materialize in 2023, it’s still worth keeping one ear to the ground on developments to privacy legislation. Remember when GDPR surprised people?
This is key to enabling organizations to drive security through the dynamic and agile aspect of human-layered security, rather than through more traditional technology- and policy-focused approaches.
A government agency will put its money where its mouth is
In July of 2022, a certain report sent shockwaves through the industry.
The report confirmed something that has been an open secret for a long time: security awareness training doesn’t change security behavior.
We know, we know. This is nothing new.
The report, “Measuring the Effectiveness of U.S. Government Security Awareness Programs: A Mixed-Methods Study”, was penned by the US National Institute of Standards and Technology (NIST).
The fuss was not about what was said. It was about who said it.
NIST is a US non-regulatory government agency. It’s responsible for providing the NIST Cybersecurity Framework—a list of recommended security controls for information systems at federal agencies.
The standards are endorsed by the US Government, and compliance with the NIST framework is a top priority for US organizations because it helps them comply with other regulations like HIPAA, FISMA, and SOX. In other words, it unlocks business.
Okay, the report told us something we already know…so what?
Here’s the prediction. The good folk at NIST aren’t just going to dump on an industry and leave them without a solution. More guidance (read: regulation!) related to human cyber risk will be forthcoming.
NIST has already released a call for comments on “Building a Cybersecurity and Privacy Awareness and Training Program”. And will follow up shortly with an initial public draft of its findings.
Organizations will be changing to adapt. They’ll either do so in an orderly manner, because they are clued in and ahead of the curve. Or, they’ll scramble, because it became a requirement and they were not prepared.
Watch this space people. Watch. This. Space.
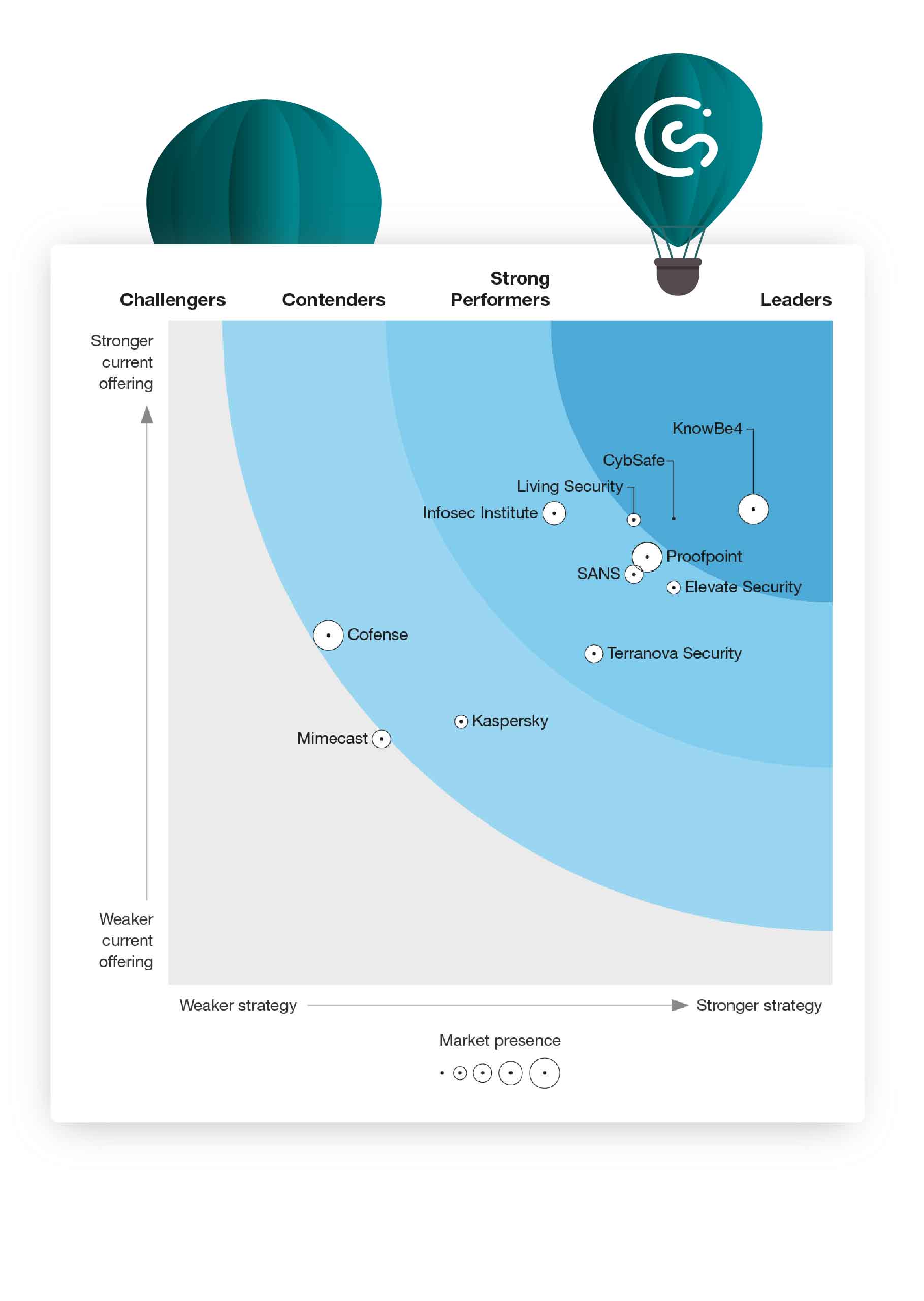
And…an industry heavyweight stirs in the deep
In 2022, Forrester led the charge away from traditional “tick-box” approaches. It ran headfirst towards more holistic ways of quantifying human cyber risk. Forrester’s recent blog, “A Sneak Peek Into The Future Of Security Awareness And Training”, gives a taste of what’s to come.
Unsurprisingly, its work aligns with the NIST findings, and shines a light on the future. Hint: it involves using tools like SebDB to measure security behaviors instead of compliance metrics.
Forrester will continue its work in 2023, no surprises there. But, they might not be alone…
In March 2022, Gartner gave its strongest indication yet that it’s taking greater interest in the human cyber risk space.
“Progressive organizations are investing in holistic security behavior and culture programs (SBCPs), rather than outdated compliance-centric security awareness campaigns.”
It’s the clearest sign so far that Gartner is solidifying its view on the changes to the market. It’s enough for them to be taking an active interest in the category, renaming it, and possibly pulling together a Magic Quadrant in the next 12-24 months.
When it happens, it will be fantastic news for the industry.
Analysts help level the playing field by cutting through vendor marketing spin (we know, we’ve been through the process several times!), giving organizations the unbiased information they need to make objective choices.
At CybSafe, we’ve never been fans of marking our own homework. It’s why we’ve always supported and engaged with Forrester’s work. We’re looking forward to working with Gartner, as and when they’re ready.
Like what you’re reading? Want more?
We’ve got you
On Thursday 8th December 15:00 GMT Oz Alashe, CybSafe’s CEO & Founder, will host a free webinar on the subject which will delve into more detail.
He’ll be joined by:
Jinan Budge, Principal Analyst at Forrester;
Lance Spitzner, Director at SANS Security Awareness;
Janet Roberts, Global Head of Security Education and Awareness at Zurich Insurance.
and Toks Oladuti, Global Delivery of Information Security at Dentons.
3. Cyber insurance
Progressive organizations—often led by transformational CISOs—make changes because they are enlightened. Everyone else changes because they are compelled!
Regulation is one compelling reason to change. Insurance premiums are another.
Cyber insurance providers are always looking for ways to reduce the risk they take on, and the risk to their customers. They’ll continue to be a primary driver for more efforts to manage human cyber risk (as they have been with other forms of risk).
Insurers will cozy up with human cyber risk vendors
In September 2022, Coalition announced a partnership with Curricula. Curricula is a security awareness training provider. And Coalition is an insurance company that looks to prevent digital risk before it strikes.
The partnership sees Coalition policyholders receiving free security awareness training directly through Coalition’s cyber risk management platform. In addition, Coalition is offering lower cyber insurance premiums to every policyholder with an active security awareness training program in place.
Another notable development has seen major Japanese insurance providers bundle KnowBe4 security awareness training into their cyber insurance offerings. We expect to see more partnerships in 2023.
You’ll start reading the small print!
Cyber insurance policies will continue to be refined. Like this year when Lloyds of London told its global network of insurer groups that as of 31 March 2023, new or renewed policies must exclude nation-state attacks.
Additional responsibility will be placed on organizations to show they are reducing risk, and not just ticking compliance boxes. We’re already seeing instances of organizations being denied payouts from their insurers.
This will continue. Insurers will stop covering for cyber negligence. The industry is too volatile to keep paying out to organizations that are not doing enough to protect their data.
Our advice? Start reading the small print! And start influencing specific security behaviors so you can prove you are measuring and reducing risk.
4. Security behaviors and human cyber risk
Before we continue, let’s stop for a breather, a cup of tea (or, if you’re stateside, a mug of Joe), and a recap.
In 2023, the rapidly changing threat landscape will drive policy makers to reconsider legislation and guidance—something the Analysts have been predicting, and calling for.
The Analysts will keep pushing organizations towards more holistic ways to manage behavioral risk.
And cyber insurers will respond by; partnering with vendors to help their customers manage risk; and by refining policy-payout terms, to help themselves.
But what does this mean for you, and your organization?
In the next two sections we’ll give it our best to keep you ahead of the pack.
Onwards!
You’re going to start feeling the pressure
Organizations will continue to invest in traditional cybersecurity awareness training, and continue to see almost zero proveable risk reduction.
As the realization dawns, a greater emphasis will be placed on people’s behavior. Progressive security teams will start asking how they can help people improve their security behaviors.
At the same time, boards will scrutinize the value of security interventions. How much money have you saved? How much risk have you reduced? Be prepared for these questions, and have your numbers ready.
The war on simulated phishing rages on
Some organizations will continue running phishing sims with no consideration for their employees’ well-being. As long as it ticks their compliance boxes.
Others will reel it in (we’re so sorry), and, with an emphasis on proving value, they’ll consider the “so what” of clicking. So what if people click? What caused them to click? What factors influenced them the most/least? What did they do afterwards?
In short, organizations looking to get more out of phishing sims will turn to more nuanced, considered approaches.
Did someone say FREE security awareness training?
We’ve said it before, and we’ll say it again. Security awareness is dead!
Don’t get us wrong though, security awareness training will still feature in advanced security awareness programmes. But, as forward-thinking vendors leave the pack and devise new ways to quantify human cyber risk, the emphasis on training will decrease.
Certain vendors—CultureAI, Elevate Security, and KnowBe4—will start offering free security awareness training. We’re already doing it. And it won’t be long before our peers follow suit.
We won’t be the only ones giving away free security awareness training. We’ll also see an increase to the number of organizations who offer security services to their customer base for free.
5. Jobs and the cybersecurity skills gap
COVID-19 changed the working world forever. For many of us, hybrid and remote work is the new norm. With this increased adoption of truly flexible working, the security stakes continue to rise.
Mind the gap
Organizations will actively look for professionals to manage their growing human cyber risk. And while Security Awareness Manager positions will be created in many medium to large organizations, a lot of them won’t be filled.
This could lead to a surge in organizations adopting security service providers, and placing more emphasis on upskilling employees.
We’ve even heard rumors some organizations are looking into the concept of ‘zero trust’ as a way of reducing human cyber risk.
Could this lead to organizations reducing their spend on behavioral risk and/or security awareness and training, in favor of implementing zero trust architectures? We’re a little less sure on this one, but we’re not ruling it out!
And finally…
Might organizations go the other way to zero trust entirely? Might we see the first Human Cyber Risk Manager positions creep onto the job market? It would make sense, given the mounting pressure to focus on measuring and improving specific security behaviors.
It would also be aligned with the changes to government guidance, and analyst positions. Either way, we have a bottle of whisky for the first person to claim the title.
Yes, you read that right. We will post a bottle of whisky to the first person to secure a job titled “Human Cyber Risk Manager”.
Beyond awareness: How to (finally) get taken seriously as a security awareness/HRM professional
Traditional security awareness training is a relic of the past. Learn how you can quantify human cyber risk and change security behaviors.
Security awareness is dead (or dying)
Traditional security awareness training is a relic of the past. Learn how you can quantify human cyber risk and change security behaviors.
A new approach to simulated phishing
Anyone can be phished and simulated phishing is not enough to protect your people. Learn four steps to an effective Agile Phishing Strategy