LONG READ
Ransomware:
The ultimate guide for 2023
Introduction
Ransomware is one of the most serious and damaging threats to cybersecurity, with its ability to wreak havoc on personal computers, corporate networks, and even public infrastructure. Part of the danger lies in its potential to facilitate data breaches, which can lead to a loss of sensitive information and further exacerbate the crisis.
But plenty of people, including inside your organization, are still asking: ‘what is ransomware?’ And even those in the know need briefings to keep up to speed on what’s lurking out there, including the potential data breaches that can result from a successful ransomware attack. These are hoping to deliver chaos in exchange for cash.
But we’ve got you covered, because we’re about to run through the nuts and bolts and then build on that with how ransomware works, what makes it such a dangerous threat, and we’ll walk you through a ransomware Most Wanted.
In other words, you’ll know what you’re up against and how best to protect your people and systems against it, including securing your data to prevent beaches.
Stay informed and stay safe.
Let’s do this!
We’ve broken our ransomware guide into the following categories:
Definition of ransomware
How does ransomware work
Ransomware stats
The history of ransomware
Ransomware’s most wanted
How to prevent ransomware
Ransomware FAQs

What is the definition of ransomware
Don’t @ us. We know it’s a cliche to start with a definition but, what can we say, it’s a very good place to start.
The definition of ransomware is a type of malicious software, or malware, that cybercriminals use to encrypt files on a device, holding them hostage until a ransom is paid.
There you go. That was over quickly, wasn’t it? It’s a short definition because ransomware can be and do a lot of things in a lot of places:
And, with the internet connected to almost every device we’ve expanded our horizons, but from now on, we’ve also opened up our entire worlds to possible ransomware threats.
The truth is this: Ransomware can be used to attack any size network. It doesn’t matter whether you’ve just got individual computers or huge enterprise servers. Either way, it can pose a huge threat to financial data and other sensitive information.
When attackers luck out with a vulnerable system, they break in using one of their favorite techniques, like:
- phishing emails with malicious attachments
- social engineering
- removable devices like USB sticks called Rubber Duckys
But there’s a lot more to understand about this cybercrime MO. Organizations and people need to protect themselves from these cyber threats with the right security measures. It’s something we’re passionate about and we’ll look at how to do that later, but first: How does ransomware work?
“Cyber criminals behind ransomware will always target organizations with low levels of IT security, and who have a need to remain operational.”
How does ransomware work
It’s important for anyone with access to your system to understand the basics of ransomware activity. Here’s our take.
So, if you’ve read this far (or if you’ve spent at least 3 minutes in a cybersecurity role), you’ll know how ransomware is an attack that encrypts data on a computer or network, often posing a threat to financial data, not to mention other sensitive information, and then asks the victim to pay a ransom.
But how does it actually work? Ransomware attackers usually follow these three steps…

Step 1. INFECT
Like any viral malware, a ransomware virus has a multitude of ways to enter and infect your system, like our good old friend, phishing emails. But we know it’s not news to you or your security team that all it takes is someone clicking on a link in a malicious email.
But that doesn’t make it any less chilling, especially when someone in your organization happens to click on the link and inadvertently welcomes the malware in like a long-lost friend, maybe offers it a hot beverage and hangs up its coat for it.
Phishing is talked about a lot, but how many of your people have heard of Remote Desktop Protocol, or RDP? Would they know what to do if cyber attackers tried to infect their computer using it?
RDP’s power move is guessing or stealing login credentials to remotely access the system. That makes downloading and executing malware a doddle.
We could go on. There are other ways, and cyber criminals are inventive finding new ways all the time. But that’s step one – infection.
What comes next?

Step 2. ENCRYPT
So, the malware has unpacked and made itself at home in the blink of an eye.
That’s when the data encryption starts.
What few people realize is–frighteningly–this only requires accessing the files, encrypting them with an attacker-controlled key, and then replacing the originals with the encrypted copies.
Experienced malware designers know they must maintain system stability, so the majority of ransomware variants are selective in the files they choose to encrypt.
Today’s variants have fewer blind spots too. For instance, to make recovery without the decryption key even more challenging, they will erase backup copies of encrypted files, leaving organizations firmly in a no-win situation.
All that’s left to do is for the ransomware to make itself known–and start making it rain!

Step 3. DEMAND
AKA the part where blissful ignorance becomes sweaty terror.
After encryption comes the payment demand. One of the most popular options attackers employ is changing the background image to display the ransom note. Another favorite is making the ransom demand via text files attached to the encrypted data.
However they’re displayed, these messages often demand a predetermined sum–usually in bitcoin or another cryptocurrency– in return for access to the victim’s data.
The now-considerably-richer attacker should then provide the means to decrypt the data, be it a copy of the symmetric encryption key itself or a copy of the private key that was used to protect it.
Did you spot the ‘should’ back there? Yeah. Let’s get onto that
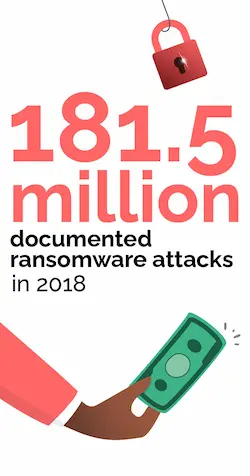
Oh look, some terrifying stats
Unless you keep up to date with cyberattack news reports it’s easy to underestimate the scope, the power, the danger of ransomware. So, just in case you were starting to get too relaxed, here’s just a flavor of the world we’re living in.
SonicWall estimated 623 million ransomware attacks throughout the course of the year 2021
The history of ransomware: Once upon a crime…
But where did it all begin? Where did it all start going right for ransomware?
The beginning of ransomware goes as far back as 1989. That’s when the first type of malicious software called AIDS Trojan (or Aids Info Disk/ PC Cyborg Trojan) was released by US biologist Joseph Popp. Popp sent over 20,000 floppy disks with the first-ever version of ransomware on them to AIDS researchers in more than 90 countries.
Once inserted, the disk would download the ransomware, ready to be activated at a later date and hold their computers hostage. That piece of malware, cheerily coined the AIDS Trojan horse (or Aids Info Disk/ PC Cyborg Trojan), is where it all began.
Ever since, cybercriminals have become increasingly sophisticated in their efforts to extort personal and financial data from unwitting tech users.
Throughout history, crypto has dominated as the primary type of ransomware. But it has a less popular sidekick: locker ransomware. And more recently Ransomware as a Service (RaaS) is proving a popular choice.
First let’s look at locker ransomware. This blocks access to your computer systems hook, line, and sinker…
This devilishly clever variation infiltrates systems using social engineering strategies and credentials that have been compromised. Threat actors then enter the system and stop you from using it until a ransom is paid.
Compared to locker ransomware, crypto ransomware is much more common. It encrypts all or just a portion of the computer’s files and asks the victim to pay a ransom in exchange for the decryption key. Some more recent variations also infect networked, cloud, and shared storage.
Ransomware as a service (RaaS), which has unfortunately grown in popularity, is where attackers pay to rent access to a specific type of ransomware, usually from its creator or developer.
Hosted on the dark web, RaaS allows criminals to subscribe to the tools of the trade rather than make their own. That means they can get down to the important business of attacking computers and databases.
The fee paid by the criminals normally depends on the features and the complexity of the ransomware. Once the attackers have gained the ransom money, the creator gets their cut, which could be as much as 20 or 30 percent.
The birth of RaaS tells us how organized ransomware is getting. And if that doesn’t hammer home how vital it is to beef up your cyber defences and human cyber risk management we’re not sure what will.
Ransomware’s most wanted
Here it is–our ransomware Rogues’ Gallery. It’s not the cutest tour you’ve ever been on, granted. But keep on checking back, because we’re tirelessly tracking new ransomware threats, so you can stay on top of thwarting them.
Maze Ransomware
Most Maze operators go the extra mile: not only do they encrypt personal data, but they also duplicate it and threaten to disclose it if the ransom is not paid. Lost data and a gigantic productivity hit are big enough risks on their own, but add data breaches and privacy violations to the mix and it’s so much worse.
Just ask Cognizant, an international IT services provider, who in April 2020 was hit with this strain. The attack exposed Cognizant’s network and could have also led to the theft of its clients’ private information.
It took Cognizant several weeks to completely restore its services, which caused many of its clients’ commercial operations to slow down or cease during that period. According to Cognizant, the hack resulted in losses of up to $70 million.
REvil (AKA Sodinokibi)
The group behind REvil AKA Sodinokibi operates as another RaaS.
According to IBM Security, Sodinokibi accounted for 37% of all ransomware assaults worldwide in 2021, making it the most prevalent malware. The Sodinokibi organization is thought to have received more than $200 million in ransom payments since it began operations, according to US officials.
Avaddon
Avaddon ransomware encrypts a victim’s files and demands payment in exchange for decryption –– so far, so standard, but that didn’t stop it from spreading far and wide.
It emerged in 2020 and is commonly spread through phishing spam email campaigns or exploit kits. Avaddon is notorious for using double extortion tactics, and the operators claimed to shut down the operation in mid-2021, releasing over 2,000 decryption keys.
Maui
The name may conjure up images of the demi-god from a Disney movie, ransomware Maui is less mischievous, more malicious.
This ransomware employs a combination of encryption techniques to encrypt specific files and is specifically designed to be manually operated by a remote attacker.
According to the FBI’s assessment, North Korean state-sponsored cyber attackers have used Maui against healthcare institutions and are expected to continue targeting this sector. The ransomware uses Advanced Encryption Standard (AES) in Cipher Block Chaining (CBC) mode with a 32-byte key generated for each encrypted file.
GandCrab
This ransomware, with its unusual moniker, was a particularly prevalent threat between 2018 and 2019.
GandCrab utilized several attack vectors, including exploit kits, malicious emails, and infected websites.
Despite its retirement, its legacy still inspires new ransomware.
CryptoWall
As impenetrable as its name suggests, CryptoWall was notorious for its sophisticated use of encryption methods and evasion techniques.
The ransomware was primarily spread through malicious emails and exploit kits.
GoldenEye
This encryption ransomware is a happy marriage of two viruses –Petya and Mischa–to encrypt data. Petya is unique because it encrypts the entire file system, not just individual files, making decryption difficult.
Initially released in a beta version called Red Petya, it was later upgraded and re-released as Green Petya. GoldenEye is the fourth iteration of Petya and employs both Mischa and Petya to create a double encryption system, characterized by its yellow and black appearance.
WannaCry
In May 2017, a global cyberattack occurred using the WannaCry ransomware cryptoworm. This malicious software encrypted data on Microsoft Windows computers and demanded payment in bitcoin as ransom.
The attack spread through the use of EternalBlue, a Windows system exploit that was originally developed by the US National Security Agency (NSA).
Petya/NotPetya
Petya infects Windows systems, encrypting the file system table and demanding bitcoin ransom to restore access.
In 2017, a new version called NotPetya used the EternalBlue exploit, developed by the NSA and also used by WannaCry, in a cyberattack on Ukraine. Kaspersky Lab named it NotPetya due to its differences.
Bad Rabbit
Bad Rabbit: cute name, deadly deeds. In October 2017, this ransomware strain from the Petya family infected around 200 businesses in Eastern Europe.
Russian media firms were the main targets, but because of the way ransomware moves over networks, other business networks in Japan, Eastern Europe, and Russia were also affected.
Drive-by attacks were used to disseminate a phoney Adobe Flash update that, when activated, would encrypt system data with RSA 2048-bit keys and demand payment.
CryptoLocker
Living up to its name, CryptoLocker was one of the first ransomware strains to utilize strong encryption algorithms, making it impossible to decrypt files without the unique key.
The malware was distributed through the Gameover ZeuS botnet and made significant headlines in 2013 and 2014.
Jigsaw
Named after the iconic character from the Saw movie franchise, Jigsaw introduces a level of malevolence rarely seen in ransomware.
It progressively deletes encrypted files every hour that the ransom isn’t paid, turning the situation into a nerve-wracking countdown for victims.
Clop
Ransom.clop relies on an RSA 1024-bit public key to encrypt data on infected machines.
There are several ways to disseminate clop. The most typical ransomware variant uses email and is frequently sent out as spam, but it can also use social engineering. It was first seen back in February 2019 in an attack by TA505.
Since then, it has become one of the most used ransomware in the RaaS market until the arrest of certain Clop associates in June 2021.
RobinHood
Since this encryption malware’s discovery in 2019, RobinHood has been linked to several high-profile attacks, targeting government organizations and healthcare providers.
While the attackers are known for their aggressive tactics and demands for large ransom payments, their identities and location remain unknown.
The ransom note left by the attackers contains a hint, with the second paragraph ending in the statement: “So do not waste your time and hurry up! Tik Tak, Tik Tak, Tik Tak!”
Are they using their ill-gotten gains to pay the bills while they learn viral dances? Who can say?
BlackCat
The BlackCat ransomware group has been targeting victims since November 2021, with over 60 organizations already affected, including a member of the Multi-State Information Sharing and Analysis Center.
The group accesses its targets using compromised user credentials and installs its ransomware payload via Group Policy Objects. BlackCat is notable for its potential links to DarkSide, its utilization of the Rust programming language, its distinct affiliate payment structure, and for launching one of the first public data leak sites.
DarkSide
They operate as part of a RaaS model and use TOR for Command and Control. DarkSide gained notoriety for the cyberattack on the Colonial Pipeline Company in May 2021, which resulted in the company paying a ransom of 75 bitcoin ($4.4 million) to restore operations.
TeslaCrypt
Contrary to what its name might suggest, TeslaCrypt doesn’t target electric vehicles. Instead, it was a ransomware variant notorious for targeting gaming files.
It was distributed through the Angler exploit kit and ceased operations in 2016.
SamSam
SamSamSamSam secretly spies on you for a certain period after being infected. The creators of this program cleverly hide their tracks. Numerous times, the assault’s original vector of ransomware infection is unclear, or certain links in the attack chain are missing.
2018 was an excellent year for SamSam. It leveraged flaws in RDP systems (Remote Desktop Protocols), Java-based web servers, FTP servers, and even brute-force attacks against weak passwords to enter and infect their victim’s systems. Ah, the memories!
LockBit
To compel victims to pay a ransom, LockBit ransomware attacks opts for what’s known “double extortion.” The tactic involves the victim paying twice, once to restore access to their encrypted files and again to prevent the exposure of their stolen data.
Some LockBit attackers leverage the Ransomware-as-a-Service (RaaS) approach, where an Initial Access Broker (IAB) obtains initial access to a targeted organization’s system and sells it to the primary LockBit operator, who then employs second-stage malware to cause further damage.
Proof that the phrase “teamwork makes the dream work” even applies to cybercrime.
Dharma (CrySiS)
Part of the CrySiS ransomware family, Dharma ransomware has been active since 2016 and employs a RaaS model. It is primarily used in targeted attacks and is manually delivered through Remote Desktop Protocol (RDP) connections using leaked or weak credentials.
Ryuk
Ryuk is a particularly dangerous family of ransomware that appeared in 2018 and is associated with “big game hunting”, where large companies are targeted. It carries a Japanese name from the anime movie Death Note, which means “gift of god.”
Russian cybercriminal group WIZARD SPIDER is believed to operate Ryuk ransomware, and UNC1878 is also known to be behind some healthcare-specific attacks.
Ryuk is able to encrypt remotely and can perform Wake-On-Lan, contributing to the effectiveness and reach of its encryption and the damage it can cause.
How to prevent ransomware:
What is the best ransomware protection?
Ransomware may not be young, but it’s an alarming threat in today’s digital world, and countless people have their data held hostage every single day.
The best way to avoid your organization falling victim to ransomware, is to help people take proactive steps to raise and strengthen the defenses.
We’re not going to tell you to install anti-virus and security software on all your devices (though you should). And we’re not going to nag you about regular and separate backups of all important files. If you’re reading this, we’d bet you’re ticking those boxes already.
But it’s crucial to understand the role that behavior plays in guarding against cyber attacks. Don’t get us wrong: people aren’t the weakest links or the strongest tool in the box. They are simply people.
Plus, scammers are nothing if not dedicated! Their day job is to make a phishing email, for example, look as real and genuine as they can, so people don’t think the ‘don’t click on unknown sources’ advice they received in their super-basic awareness training applies here.
Speaking of super basic training, boring compliance frameworks that tick legal obligation boxes have overstayed their welcome.
They don’t help you fight against real world cyber attacks. Compliance as a metric for success guarantees one thing alone: safety blind spots, which leads to a false sense of security.
These out-of-date systems don’t actually influence long-term security behaviors and, therefore, don’t reduce human cyber risk.
So, what does work?
The key to transforming security behaviors in your organization is this: It starts by exploring what a modern security solution looks like.
We know certain security behaviors sit at its core. When people create strong passwords, add multi-factor authentication, and protect their online privacy, they are strengthening the all-important human layer of security.
And when organizations guide people on how to stay secure with remote work, how to use a VPN, make frequent backups, and ensure auto-updates are on, they are making it harder for criminals to get through.
Your people’s experiences matter. So it’s vital to get those phishing simulations right, and to do all you can to influence healthy long-term security behaviors.
It’s what will keep you ahead of the ever-evolving compliance standards, and help you fortify your human layer of security and prevent ransomware.
Ransomware recovery:
How to get rid of ransomware
Your data is precious to attackers, so they don’t make it easy to recover ransomware data. The malicious and encryption efforts the malware uses aim to make recovery very tricky.
But, fortunately, there are ways that victims can recover ransomware data without paying a fee.
Methods of ransomware recovery can include utilizing false decryption tools or manual methods such as restoring backed-up files with updated anti-ransomware software.
Some attacks buckle upon running an antivirus scan (though you definitely shouldn’t base your cybersecurity policy on this potential stroke of luck), or sometimes restoring your computer to an earlier version works.
Wise to this, some attackers will delete these backup files to keep the upper hand. So, the best place to start with your ransomware incident response is to find out what type it is and then you can move on to how to remove it.
No matter what steps you take, having a thorough knowledge of ransomware, in general, is key to thwarting future attacks.
That said, information is only a part of the picture. Influencing people’s security behaviors is the single most effective way to tip cyber risk in your favor, rather than in the favor of greedy cybercriminals out to spoil your day.
Empower your people and reduce risk
Looking to upgrade your organization’s cybersecurity practices?
One thing’s for sure: traditional security and awareness training doesn’t change risk. That’s because it doesn’t change the way people act in the long term. And that’s the key – influencing people’s behavior, so they make good security choices every time.
We believe that people play a crucial role in protecting against cyber threats, which is central to our ransomware report. It provides valuable information to influence security behaviors and reduce cyber risk. It’s an essential tool for anyone staring down ransomware or other risks. So, everybody, really…
Download Our Ransomware Report to Strengthen Your Cybersecurity Defenses.
Ransomware FAQs
Security awareness is dead (or dying)
Traditional security awareness training is a relic of the past. Learn how you can quantify human cyber risk and change security behaviors.
A new approach to simulated phishing
Anyone can be phished and simulated phishing is not enough to protect your people. Learn four steps to an effective Agile Phishing Strategy
Ebook: Ransomware is real
What you – and your people – do need to understand about ransomware (and any malware!) is how to spot it, and stop it. And importantly, not to be afraid of it. If you are ready to ditch the fear and find an approach that works, this Ransomware is boring eBook is what you need! Download today.