Ah, don’t you love living in the world of cyber threats? Where traditional security measures won’t be enough to keep your organization safe. Lovely here, isn’t it?
Why didn’t we all go with our five-year-old self’s career aspirations and go into donut testing?
For what it’s worth, we think you’re nothing short of a hero. With cyber threats evolving and increasing in frequency every day, the threat to organizations is, well, prett-ay daunting. And you’re reading this because you care.
It’s people like you who make us want to get up in the morning.
Anyway, back to the topic in hand. You know it’s important to equip your people with the knowledge and skills they need to stay secure. In fact, it’s more important than it’s ever been.
And you want to make sure your training program actually reflects what’s going on out there, right?
And you’ve got questions. Things like:
What should cybersecurity awareness training courses in 2023 cover?
Why is staying up to date with the latest threats important in cybersecurity?
Why should everyone understand how social engineering works?
Well, good news. We’re about to take a look at the 10 key cybersecurity topics that you can’t afford to miss from your cybersecurity awareness training courses in 2023.
This short read is the perfect starting point—the warm-up, if you will. And our 2023 security awareness predictions report is the ultimate headliner.
You’ll scream, you’ll cry, you’ll hold your lighter aloft.*
*Results may vary.
Ready? Here they come.
1. Threat intelligence
Staying on top of the latest threats is critical to keep your organization safe. 70% of cybersecurity professionals surveyed for our predictions report said they plan to invest more in threat intelligence in the coming years.
Threat intelligence is a powerful tool that helps organizations to anticipate, detect, and respond to cyber threats. Cybercriminals are always coming up with new ways to breach organizations, so it’s essential that people are trained to identify potential threats and take appropriate action.
Threat intelligence training should cover the latest trends in cybercrime, including new attack methods, malware, and ransomware. The training should also give people the tools and techniques to spot cyber threats.
With the right threat intelligence training, you’ll position people where they should be—as an integral part of an organization’s security infrastructure.

3. Password management
Passwords are the first line of defense against unauthorized access to sensitive data. And that means password management is an essential part of any worthwhile cybersecurity program.
Do your people know how to create strong passwords? Do they understand the importance of not sharing passwords? Do they know how to manage passwords securely?
Password management training should cover the use of password managers, multi-factor authentication, and best practices for creating strong passwords.
And, vitally, the training should emphasize the importance of changing passwords regularly—and why we don’t reuse old passwords across different accounts.

4. Phishing awareness
So, yes, phishing attacks are very common. And because of your job role, maybe you never stop thinking about them. In fact, maybe you even dream about them.
But how sure are you that others in your organization would spot a cybercriminal trawling for sensitive information?
It’s essential to train people on how to spot phishing emails and what to do if they receive one. Training should cover different types of phishing, like spear-phishing and whaling, and how to report a phishing email.
And they’ll need to know how to verify the authenticity of an email before clicking on any links or downloading any attachments.
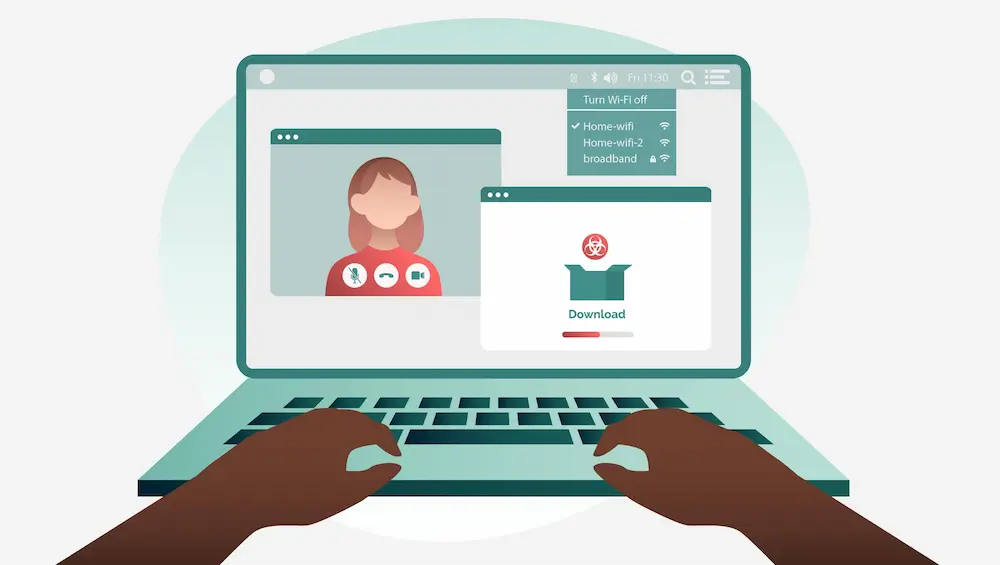
5. Malware protection
Malware is a royal pain. It’s designed that way. And people need to know about it to stop it damaging or disrupting computer systems.
Training on viruses, worms, Trojan horses, and spyware will help equip people to recognize and avoid it, how to report it if they encounter it, and how to protect against it.
People need to appreciate that updates and security patches help prevent malware from taking hold. And vitally, the reasons we don’t just download any old file from any old place on the internet.
6. Mobile device security
Mobile devices are becoming increasingly popular targets for cyber criminals.
So, people need to know how to secure them properly.
They’ll need to know best practices for using mobile devices securely. That includes how to protect sensitive information stored on them, how to use strong passwords, and how to avoid risky behaviors like using public Wi-Fi networks.
It’s also important to have a plan in place for lost or stolen devices. Would someone know what to do if their device is lost or stolen? Could they remotely wipe data if they needed to? Would they know how to report the loss?
7. Cloud security
Cloud computing is ever more our go-to for storing and accessing data. But do your people know how to use it safely?
They need to understand the risks that come with cloud computing and how to handle them like pros.
So your training program will need to cover how to use cloud services securely. That’ll include how to protect login credentials, how to avoid sharing sensitive data in public cloud environments, and how to use encryption to protect data in transit and at rest.
8. Data protection
The goal behind so much security behavior is of course safeguarding the data we hold.
People should be trained thoroughly on this critical topic. To keep your organization safe they need to feel confident in how to handle sensitive data, including how to securely transfer it and how to store it safely.
Oh—and they should learn about best practices for using strong passwords, encrypting sensitive data, and backing up data to prevent data loss in case of a cyber attack.
9. Incident response
Much training covers how to avoid successful attacks … and it stops there.
Do people outside of your team know how to respond to a cybersecurity incident? This is a vital topic. You need to cover how to recognize and report security incidents, including who to contact and what information to provide.
People should also be trained on how to limit damage and restore normal operations as quickly as possible.
Sure, having a well-documented incident response plan in place can help to reduce the impact of an incident. But people should be trained on how to follow that plan, in case of a breach or attack.

10. Continuous learning
Cyber threats are constantly evolving.
Just like a TikTok feed, it’s never ending.
So, it’s important that people stay up-to-date with the latest news and best practices.
Cybersecurity awareness training should be just as constant. But instead of recycling the same old same old, it should throw out regular updates and refresher courses to keep everyone engaged and informed.
A culture of continuous learning and improvement sounds ever so grand, doesn’t it? But it’s exactly what you need to create a more security-conscious organization.
A strong cybersecurity culture is guaranteed to bring down the risk of cyber attacks and breaches.
We promise that by empowering people with the knowledge and skills they need to stay safe online, you can create a stronger security posture and better protect themselves against cyber threats.
Before we end the lesson. . .
So, where are we at?
Cybersecurity threats are constantly evolving (and increasing in frequency). And traditional security measures are no longer sufficient to protect organizations from those threats.
Still, there’s no getting away from it: Education is a crucial part of maintaining a secure organization.
Your 2023 cybersecurity training needs to cover these topics. Otherwise, instead of training, you might as well just put Frozen on, and have an office singalong. At least you can go down singing.
But instead, we’re going to suggest you serve up an all-bases cybersecurity training program.
You’ll ensure that your people are not only knowledgeable but confident too in protecting themselves and the organization against cyber threats.









2. Social engineering
Cybercriminals love social engineering almost as much as they love making your life a misery.
It’s a favorite tactic because of how well it works. When they need to trick people into revealing sensitive information or causing major headaches for organizations, it’s the go-to technique.
And one thing you need to take into account is how these tactics are becoming increasingly sophisticated—and difficult to detect.
So, give your people the best chance. Show them how to recognize and resist social engineering attacks. They should know how to spot suspicious messages, emails, or calls.
This training should also cover the different types of social engineering attacks, like phishing, pretexting, baiting, and tailgating.
And remember, people need to know how to report a social engineering attack and who to contact if they suspect they’ve been targeted.