“Don’t tell me not to click when clicking is my job!”: Saving people from security awareness training
We’re born knowing very little, yet we need a lot of knowledge to live our lives. Learning is, therefore, a huge part of being human…and it’ll never not be a part of managing cyber risks.
That said, we need to talk about cybersecurity education—or more specifically security awareness training. Why are so many organizations still relying on outdated, ineffective programs…and what can they do instead?
At IMPACT 2024 USA, we tasked a powerhouse panel of three experts to tackle this issue head-on. Armed with both inspiration from the conference and their own varied experience, our wise minds unpacked the critical themes within security awareness training.
More importantly, they dug into the “how”, translating these insights into actionable strategies for organizations everywhere.
Wait, what is IMPACT?
Glad you asked. IMPACT is a conference where the human risk management community gathers to dig into the juiciest insight from recent research on human risk management. It’s hosted by CybSafe and supported by some of the biggest players in the industry.
But 2024 was double the fun and double the…well, IMPACT! (Is this thing on? 🎤)
IMPACT not only returned to the UK for the fourth year running, but also launched a smash-hit inaugural event in the US – IMPACT 2024 USA.
Whichever side of the Atlantic you’re on, IMPACT is a seriously valuable opportunity for anyone thinking about human risk. So, if that’s you, join our mailing list and make sure you don’t miss out on IMPACT 2025.
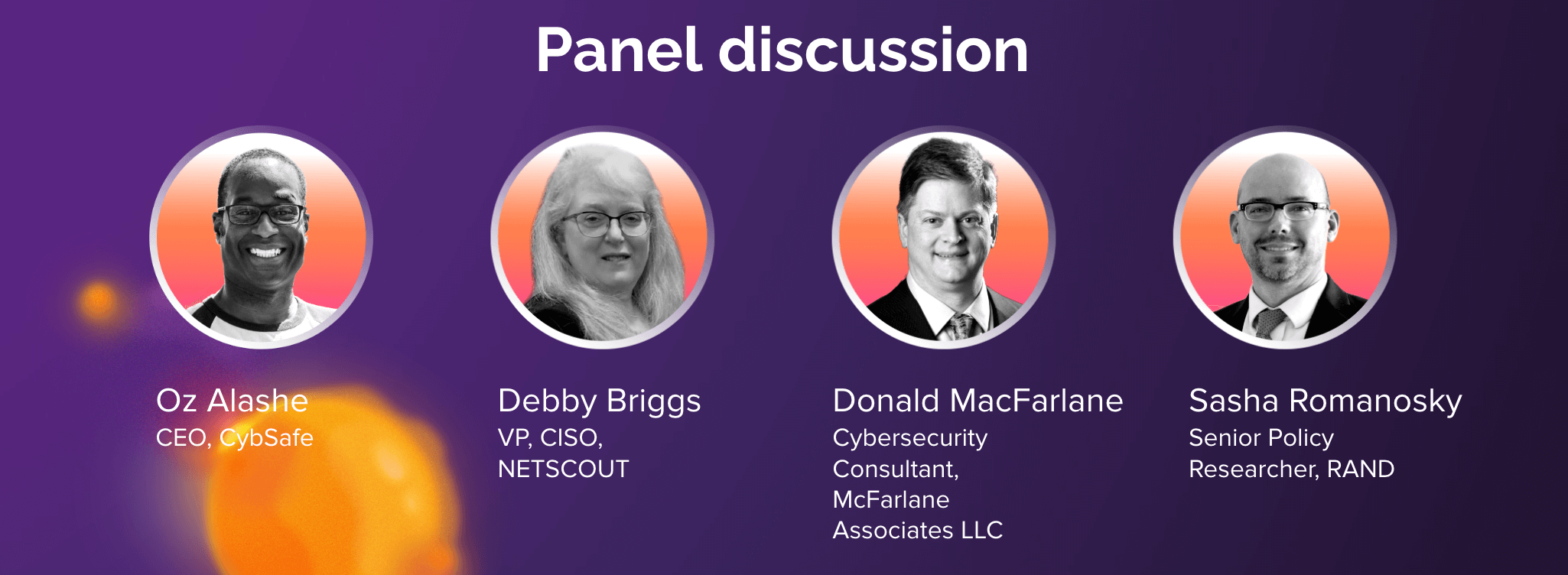
Time to meet the panel:
-
- Deb Briggs is VP, CISO at NETSCOUT, a worldwide R&D company. She’s been there for over twenty years, and was the first-ever CISO there. Security awareness is part of her role’s remit.
- Donald McFarlane is a cybersecurity consultant at McFarlane Associates LLC. He’s an experienced CISO, a hacker, and, he says, a “cybersecurity troubleshooter for businesses”.
- Sasha Romanosky is a Senior Policy Researcher at RAND, where he does policy research in cybersecurity, including cyber insurance, cybercrime, law and economics.
- And the session conversation was facilitated by CybSafe’s very own Oz Alashe, CybSafe’s CEO and founder.
Enough preamble. Let’s go deep on the discussion.
Part 1: Learning and behavior
The cybersecurity world is waking up to the fact that traditional security awareness and training (SA&T) doesn’t meaningfully change people’s security behaviors.
As Oz put it when the discussion got under way: “One of the things that I think is really exciting about the community right now is we’re spending a lot more time thinking about behavior and of course knowledge and behavior are of course two quite different things—there are doctors who smoke! … The real question is whether the behavior changed.”
Our panelists got into SA&T’s shortcomings, and how learning experiences can be better designed and delivered. What qualities do today’s training programs need? And what do we need to understand about human behavior if we want to craft effective training that resonates with people, and addresses their cognitive biases?
Here’s how it happened.
Awareness is not the (whole) solution (and maybe it’s not even the problem!)
So, like Oz said, if doctors smoke, awareness isn’t the be-all and end-all. Better awareness does not equal better behavior. Yet it’s better (read: more secure) behaviors that will reduce human cyber risk.
That means you can’t understand human cyber risk if you don’t understand human behavior.
Insider threats aside, no one means to click on a bad link. They click on them because they’re human. They get tricked, they make mistakes, they get pressured. Training needs to take that into account.
There was a panel-wide consensus on the limitations of traditional awareness training, which pays very little attention to behavioral science. The panel agreed that there was a need for a more comprehensive approach than the old-school one-size-fits-none approach.
But that’s not to say that training should be binned entirely. “Cybersecurity awareness training—it works,” Deb asserts. “It’s not the only tool, it’s not the best tool, but it is a tool. I think sometimes that’s all we think about, is we’ve got that one tool and that is what we have to do. We have to move beyond that.”
So, where does traditional training get it wrong? “We can’t just have one training for thousands of people,” says Deb. “Everybody is unique, people have different training styles, people have different roles, people are at different places in their life … I think it’s important that you try to meet people where they are, not put them in front of a screen, watching them click for forty-five minutes.” (Oh, and don’t worry, we’re getting on to personalization next.)
Donald raised a valid question: “Are we solving the right problems? Do we know what the problems are? I would put it to you that there is a quite significant proportion of security engineering that goes on in industry today where we are solving the wrong problem, and we don’t necessarily even understand what the business problem is we’re trying to solve for.”
In other words, is fixing awareness training kind of missing the point?
It’s easy to sit back and bombard people with the entire textbook. But we need to be context-informed and person-centered. The community needs to design—and deploy—interventions that focus on user behavior and skills development.
Make it personal and people-centric, with a side of metrics
If something’s not personal and relevant it’s, yep, sing it with us, impersonal and irrelevant.
Maybe that explains why putting the person at the heart of the interventions was another important thread in the conversation.
As we touched on above, security awareness training often has a one-size-fits-none approach. You herd everybody in front of a screen, show them an elearning package, give them a little quiz, and hope for the best.
Deb understands the importance of honoring people’s preferences and learning styles: “A lot of cybersecurity awareness training is 45 minutes in front of a screen, click click click click click click click … We need to ask people how they want to receive the information, how they will retain it.”
Deb recognizes the reality of any workforce: People have different learning styles, they have different risk tolerances, and they have different job functions.
The conversation touched on how training needs to connect with users on a personal level. Instead of generic threats, training should focus on real-world scenarios and the potential impact on individuals and their loved ones.
Donald was particularly passionate about metrics: “I think we could all use more information, and obviously more evidence, about what kinds of activities does a user participate in throughout the course of a day, and which of those could be influenced by the organization—obviously in a way that’s ethical and privacy-preserving and the rest of it … but I think this is a good start.”
“Let’s understand what the real problem is we’re solving for with these solutions, and let’s pick the metrics accordingly,” Donald says.
Sasha weighs in here too: “Part of my interest recently has been in understanding the role of humans in influencing a firm’s overall cyber risk. What is the role of humans, of employees, in contributing to that firm’s cyber risk? What I started to think about was of all the activities that employees of an organization could engage in, which of those would be awareness and which of those would be skill-based? Is that a thing—can we enumerate all these activities?”
The panel’s consensus is clear: Intuition’s seriously overused in cybersecurity … and it’s seriously overrated. We often think we know what works, and how much impact an intervention’s had, but there’s very little data to back that up. How do you know if your investments in security awareness training are actually having an impact?
Without metrics, without data science, you won’t.
The bottom line? Effective training should be engaging, user-centric, and measure the impact on cyber risk.
Balancing awareness and skills
So, awareness is important, but it’s only one component. What else?
Skills. The discussion highlighted the importance of equipping people with practical skills to identify and respond to cyber threats. The more the training focused on real-world scenarios, the better.
Deb used phishing simulations as an example. Should we penalize people when they’re not great at avoiding phishing emails? She poses a critical question: “If they didn’t get the training the first time and I send them to the training second time, am I going to change the behavior?” And is remedial awareness training really going to change that?
What should happen instead? Deb reflects on an alternative: “Rather than throw shame on you, what about for the next four weeks we continue to give you phish and when you click on a phish, rather than just hammering you over the head, we’ll give you examples and then tell you what you should have seen.”
It boils down to this: Awareness training is telling people the theory of something. Skills-based training is about letting them practice it. And … the ability to spot phishing is just one of over a hundred security behaviors!
Part 2: Culture and communication
Next, it’s time to look at the panel’s thoughts on fostering a strong security culture in an organization. The panel got into the importance of leadership setting the tone, clear communication of security risks, and encouraging people to report suspicious activity.
The tone from the top
One thing kept coming up again and again during the discussion: Leadership plays a critical role in fostering a culture of security. Management needs to support people in making secure choices. Management needs to empower people to challenge suspicious activity.
Take tailgating (i.e. following someone else through a secure door) as a real-world example. It’s not enough to stop once people know how to use a door, Donald emphasizes: “What I’m hoping to achieve when I contemplate how to train people is not simply the mechanics,” he says.
“It is making them know that it’s okay to stop somebody and ask them who they are and why they’re there, that management is going to not only be okay with that, they’re going to have your back—they’re going to praise you for it.”
But what if management expects you to bend or break the rules for them? Deb has witnessed this before, where security staff (particularly junior roles) come under pressure from leadership to go ahead without the senior member verifying their credentials.
“When you tell a VP that you are not going to do something, most young people in the industry are afraid of the title and … they will break every rule to get them off the phone, to make them happy.”
What does she do when this happens? She tells the junior member to send the VP to her, have the VP scream at her, not them. It’s important that no one is above security protocol, regardless of title. It’s important that senior management respects this, she explains.
Donald summed it up nicely: “It’s the opportunity for tone from the top. It’s the opportunity to take that lesson to say, ‘Mea culpa, I am now using a more complex password.’ or ‘It is okay to slow down and to do security better, to to do authentication better.’”
Clear comms, real conversations, can’t lose
Jargon can make us feel big. But how does it make our workforce feel?
We get it. It’s tempting to use it to assert our expertise … but it’s a short-sighted habit.
According to the panel, we need to avoid jargon and technical terms where possible. Doing so helps people get the information and skills they need. The message works best when it’s clear, succinct, and when it resonates with the lived experiences of your audience.
A really interesting point that came up was around terminology. Does everyone need to know about every single type of phishing tactic … or do they just need to know about social engineering that drives all of them?
It’s not just about concepts, but messaging, Deb highlights. “I think that words mean things,” she says. “A lot of times, what we educate people on is counter to how people actually act … Don’t tell me not to click anything if my job is to click all day long … We have to find a way to better reach people in ways that actually logically makes sense.”
Deb avoids dishing out commands from on high, instead opting for real, non-expert-led conversations. How did this come about? “At times people think I sit in my office, the ivory tower, and just make up policy just because I like to. It’s really interesting.”
Instead, she tries to bridge the gap in a very human way by ‘explaining why’, in a relaxed environment, in a back-and-forth conversation.
The crucial component? Snacks. “I offer free popcorn. I bring in a popcorn machine and I put what I’m trying to get across is a sticker on the popcorn cup. People love free popcorn, and if I offer free food people come. You see the people and you talk to them, and it’s not just like, ‘You shouldn’t click on links,’ you’re actually talking to them and understanding their point of view, what they are seeing, what’s important to them, how you can relate to them. I think that’s what we need to start doing more of.”
Circling back to the tailgating example, Deb concludes: “Sometimes training isn’t so much about teaching them something new, it’s letting them know it’s okay to question.”
Part 3: Zooming out: Context and broader issues
No industry is an island. Any cybersecurity practitioner is wise to remember they’re part of a bigger picture, that there’s a whole world out there. Running an organization is about making difficult trade-offs, every day.
Meanwhile, there’s a disconnect in the cybersecurity community. Research and practice seem almost at cross purposes. Or are they? Let’s get some perspective from our pro panel.
The broader context of cyber risk
It’s easy to ignore things outside of our own particular missions and goals. But we can’t—not in the long run. This was something our panel was keen to address. Their discussion acknowledges that cybersecurity is just one of many risks individuals and organizations face.
Sasha shot from the hip: “This is a little blasphemous for a cyber guy to say, but cyber is not the end all, be all. It is not the only thing that we are concerned about, right? … Cyber is just one of many competing interests, both for us as individuals, as consumers, as users, and for firms too.”
Everything is a trade-off, he reminds us, so “we shouldn’t begrudge them for not spending every dollar they have in cybersecurity. They have a portfolio of risks just like we have a portfolio of risks. Yes, cyber is important, but it’s not the only thing.”
What does this mean when it comes to education? Security won’t be the most important thing to people, and that’s okay … maybe it’s even right. Deploying dull, dated training and expecting people to pay attention just because ‘this is important!’ is doomed.
Research vs. real world: The tension is palpable
The discussion called out the tension between the need for specific research and the need for practitioners to connect with real users, in real-world contexts.
Finding a balance between these approaches is essential … but not necessarily simple.
Oz chimed in with an important point here: “On one hand we’ve got practitioners who are literally trying to connect with and communicate with and help real people who’ve got real jobs and real contexts that are relevant to them.”
“On the other, …” he continues, “… we’ve got those of us who are also maybe trying to research things, and you’ve got to be quite specific when it comes to research, because otherwise you make blanket statements or blanket assumptions.”
“So whereas it might be absolutely appropriate to talk to [non-experts] about social engineering and not confusing them with the different types of social engineering, when it comes to researching it might be really rather important that you’re thinking about the different types of social engineering, because maybe they’re not all the same and maybe the things we need to discover are not all the same. This is not a bad tension if we acknowledge it exists.”
Cybersecurity research and practice have distinct differences, different priorities sometimes, and different styles and approaches. And that’s okay.
Surface: scratched
We’ve gone deep on this discussion. But this conversation is only a small part of what made IMPACT 2024 so insightful and inspiring.
That’s why we invited a plethora of clever-clogs from the human cyber risk field to spill the beans at IMPACT. To enlighten the community and to provoke thought, and maybe raise a few laughs too.
Missed the fun? Download all the unmissable insights and headlines in one place – IMPACT: The Findings!
It’s your cheat sheet to the biggest takeaways in human cyber risk. The latest academic research on the human aspect of cybersecurity. No filler, all hits.
It covers:
-
- Finding and addressing vulnerabilities in your security strategy,
- Why we get in our own way when trying to help people act safer,
- Why cybersecurity is so messy…and why that’s okay!
- The huge divide in our community, and how we might be able to close it,
- And so, so much more.
Get your hands on it right now, right here.