
Account Compromise
Account compromise happens when unauthorised people access them.
Behaviours
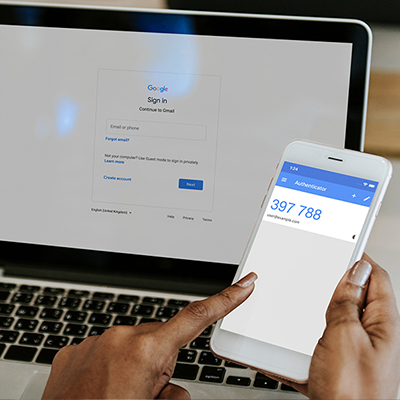
SB001: Enables multi-factor authentication for workplace accounts
Multi-Factor Authentication (MFA) is the process of signing in to an account using more than one piece of ...
SB003: Uses a strong password or passphrase
Strong passwords/passphrases should be used for all accounts containing sensitive data, such as workplace ...
SB005: Uses Single Sign-On (SSO)
Single Sign-On reduces login friction and can encourage stronger password/passphrase use.

SB007: Checks whether passwords (or other personal data) have appeared in known data breaches
Tools such as haveibeenpwnd.com can be used to check if passwords (or other personal data) have been leaked in ...

SB008: Checks whether personal information shared publicly online could be used to answer security questions
Security questions provide a recovery option for online accounts. Their answers must be protected. Before posting ...

SB009: Ensures online accounts that are no longer needed are de-activated
Dormant accounts may still hold or provide access to sensitive data. Security teams should be notified when ...
SB010: Does not share passwords
Password sharing increases the likelihood of an account being compromised. Passwords should not be shared. Any ...

SB013: Reports known or suspected security incidents
Reporting known or suspected security incidents helps protect people as well as their place of work. If the ...

SB014: Asks security professionals for help with security issues
Asking for help can help people learn. Security professionals can advise on how best to approach and resolve ...

SB015: Completes assigned security awareness training successfully
Security Awareness training is an important part of organisational security. Completing awareness training ensures ...
SB016: Does not re-use passwords between accounts
Using unique passwords ensures that if one of your passwords is leaked, not all your accounts can be accessed.

SB022: Installs antivirus on all compatible devices
Antivirus/Endpoint protection programs provide excellent coverage against known online threats. They should be ...

SB022a: Installs antivirus on all compatible workplace devices
Antivirus/Endpoint protection programs provide excellent coverage against known online threats. They should be ...

SB022b: Installs antivirus on all compatible personal (i.e. non workplace) devices
Antivirus/Endpoint protection programs provide excellent coverage against known online threats. They should be ...

SB023b: Enables firewalls on all compatible personal (i.e. non workplace) devices
A firewall is a set of virtual rules that help prevent malicious applications from communicating with a device. ...

SB030: Follows advice given in security warnings
Security warning alert to potential harmful activity, like when a malicious website is visited. The advice should ...

SB048: Uses a privacy screen when working with sensitive information in shared spaces
Privacy screens prevent opportunistic onlookers from viewing sensitive information. They should be used when ...

SB055: Reads organisational security policy
Security policies help reduce risk by increasing the chance that people will understand what to do to keep their ...

SB056: Highlights security controls that prevent or disrupt ability to work sensibly
Sometimes security controls can prevent or disrupt job activity. In these instances controls may be ignored to ...
SB073: Sets account passwords with network provider
Criminals with access to network providers can launch SIM swap or mobile phone number porting attacks. Agreeing a ...
SB074: Uses a private browsing on shared devices
If workplace devices are shared between colleagues, private browsing should be enabled by default. This means ...

SB081: Checks instant messages for signs of deception
Criminals will often use instant messaging (e.g. Whatsapp, Facebook and Slack) as an attack vector. Unexpected ...

SB087: Reports suspicious messages (e-mails, texts, phone calls)
Suspicious messages received via email, text or phone should be reported to a single point of contact. This allows ...

SB088: Checks emails for signs of deception
Criminals will often use emails as an attack vector. Unexpected emails should always be checked for malicious ...

SB089: Does not share MFA codes
Doesn't share MFA codes (including verfication codes and OTPs) with other people, preventing them from accessing ...

SB093: Deletes old personal online accounts if no longer used
Deleted online accounts and "zombie" apps that no longer used. These accounts are a security risk as they often ...

SB105: Uses a security key
Security keys are USB keys or dongles that work as an advanced form of multi-factor authentication. Using them ...

SB150: Does not use a password that has been compromised in a data breach
Passwords that have been compromised in data breaches are often shared or sold amongst cyber criminals. Other ...

SB152: Does not log in with shared credentials
People should not log into their accounts using credentials that have been shared with other people. Doing so can ...

SB156: Discloses credentials to a phishing site
Disclosing credentials to a phishing site places the individual and their organisation at risk of account ...

SB156a: Discloses credentials to a simulated phishing site
Disclosing credentials to a phishing site places the individual and their organisation at risk of account ...

SB159: Does not click a phishing link
Clicking on a phishing link could lead you to a fake website that asks for private credentials, or tricks you into ...

SB159b: Does not click a simulated phishing link
Clicking on a phishing link could lead you to a fake website that asks for private credentials, or tricks you into ...

SB161: Reports a suspected phishing email
Reporting phishing emails notifies IT or security teams that employees are being targeted by cyber attackers. ...

SB161b: Reports a simulated phishing email
Reporting phishing emails notifies IT or security teams that employees are being targeted by cyber attackers. ...

SB163: Does not open a phishing email
Some phishing emails include macros that autorun on opening. Even though these cases are rare, if possible it is ...

SB163a: Does not open a simulated phishing email
Opening a simulated phishing email informs the IT or security team that employees might be at risk of taking ...

SB164: Does not open an attachment in a phishing email
Opening attachments on phishing emails could lead to malware infections and cyberattacks.

SB164a: Does not open an attachment in a simulated phishing email
Opening an attachement in a simulated phishing email informs the IT or security team that employees might be at ...

SB167: Reports a suspected phishing message
Reporting suspected phishing messages notifies IT or security teams that employees are being targeted by cyber ...

SB167a: Reports a suspected phishing message in Slack
Reporting suspicious Slack messages notifies IT or security teams that employees are being targeted by cyber ...

SB167b: Reports a suspected phishing message in MS Teams
Reporting suspicious messages in MS Teams notifies IT or security teams that employees are being targeted by cyber ...

SB173: Does not use work email addresses for non-work purposes
Using work email for non-working purposes increases the chance that the email might be compromised in a data ...

SB175: Does not log in from a rooted mobile device
Gaining root access ('rooting', also known as 'jailbreaking') on a mobile device is akin to running Windows as an ...

SB177: Does not lose device through theft or negligence
Losing devices containing sensitive information through theft or negligence increases the likelihood of cyber ...

SB177a: Does not lose mobile device through theft or negligence
Losing a mobile phone or tablet containing sensitive information through theft or negligence increases the ...

SB177b: Does not lose laptop/desktop through theft or negligence
Losing laptops/desktops containing sensitive information through theft or negligence increases the likelihood of ...

SB178: Does not share a desktop device
Sharing a desktop device allows someone else to have access to your personal and/or company's confidential data.

SB192: Does not disable MFA
Disabling MFA increases the risk of an unauthorised person gaining access to your account if they know your ...

SB192a: Does not disable MFA on Slack
Disabling MFA on Slack increases the risk of an unauthorised person gaining access to your account if they know ...

SB192b: Does not disable MFA on Microsoft 365
Disabling MFA on Microsoft 365 increases the risk of an unauthorised person gaining access to your account if they ...

SB192c: Does not disable MFA on Google Workspace
Disabling MFA on Google Workspace increases the risk of an unauthorised person gaining access to your account if ...

SB195: Completes policy attestation
Most organizations today have multiple compliance requirements and contractual obligations that require all ...

SB198b: Does not use unapproved desktop or laptop for work purposes
Using unapproved desktops or laptops for work purposes increases security risks. This could be for a variety of ...

SB203: Uses biometrics to access online account
People can access devices and accounts with biometric information (e.g. a fingerprint or facial scan). The unique ...

SB204: Uses biometrics to access mobile device
People can access devices and accounts with biometric information (e.g. a fingerprint or facial scan). The unique ...

SB209: Uses a stand-alone password manager application
A password manager is an application that securely stores passwords. Some password managers also create and enter ...

SB210: Saves passwords or passphrases into a browser
A browser-based password manager is an application that securely stores passwords. Browsers often create and enter ...
Case study
Sarah Morrison
In 2019, Sarah Morrison found out why reusing passwords is such a bad idea. It cost her $13,000.
Her ordeal started with an email. The email concerned a takeaway she’d “ordered” 3,000 miles from her home in New York.
Sarah thought little of it. She notified Grubhub of the charge, which Grubhub promptly refunded. Just to be safe, Sarah also changed her Grubhub password. But the precaution wasn’t enough.
Five months later, Sarah logged into her bank account and realised she’d lost $13,103.91. Sarah had reused the compromised Grubhub password to protect her online bank account. Which, of course, wasn’t much protection at all.
It took Sarah several stress-ridden months to regain full control of her accounts. The trouble could have been avoided if she’d used separate passwords for her individual accounts.
Sarah could have also turned on two-factor authentication as an extra security layer.
“I really should have bothered!” says Sarah. “So should you.”
Claire Pearson
In April 2017, Claire Pearson watched as a £71,000 inheritance from her late father was stolen from her account.
It started with a text message from her bank informing her of suspicious account activity. Worried about possible fraud, she called the “fraud prevention helpline” mentioned in the text... without checking the identity of the sender.
After a quick chat, Claire shared her account details and password and was told she’d receive a new card within three days. However, when she called her bank back – this time using a saved number – she realised she’d been tricked.
Despite her efforts, Claire could not recover all her money. In retrospect, Claire wishes she’d verified the fraudulent text by calling her bank using the number she had stored in her phone.
The incident could also have been avoided had Claire realised that real bank officials never ask for account passwords.
Twitter Hack, 2020
In July 2020, various high-profile celebrities and companies tweeted a link to their followers. The tweets asked followers to send in Bitcoin payments, then watch as the payments were doubled then returned.
The tweets were fraudulent, posted by hackers who were about to earn $120,000 through one of the biggest account compromises Twitter has ever known.
The hackers breached 130 Twitter accounts in total, including those of Barack Obama, Elon Musk, Kanye West, Bill Gates, Apple and Uber. Twitter called the hack an elaborate case of social engineering.
In response to the breaches, Twitter restricted password resets and temporarily restricted verified accounts from tweeting.