Security has always told a simple story: bad actors attack, defenses protect, and when those defenses fail, bad things happen.
But that story misses something important. …People.
Not people as victims. Not people as the weakest link. Not people as users of the system, but as users within the system, and a core component of the system itself.
Pressure, not just attackers
Every incident begins with pressure.
Sometimes that pressure comes from outside. A cybercriminal wants money. A nation-state wants secrets. A fraudster wants access. These are the threats security teams have always understood.
But pressure also comes from within. A finance manager racing to close the quarter. A support agent juggling too many tickets. A new starter unsure which process to follow.
These aren't attackers. They're just colleagues, doing their best, under conditions that make mistakes more likely.
And pressure also comes from above. Regulations that demand reporting. Policies that conflict with workflows. Audit deadlines that compress timelines.
No malice here. Just the weight of obligation meeting the friction of reality.
A CISO can lose sleep, hair — or indeed their job — over any of these. So all of them belong in the threat model.
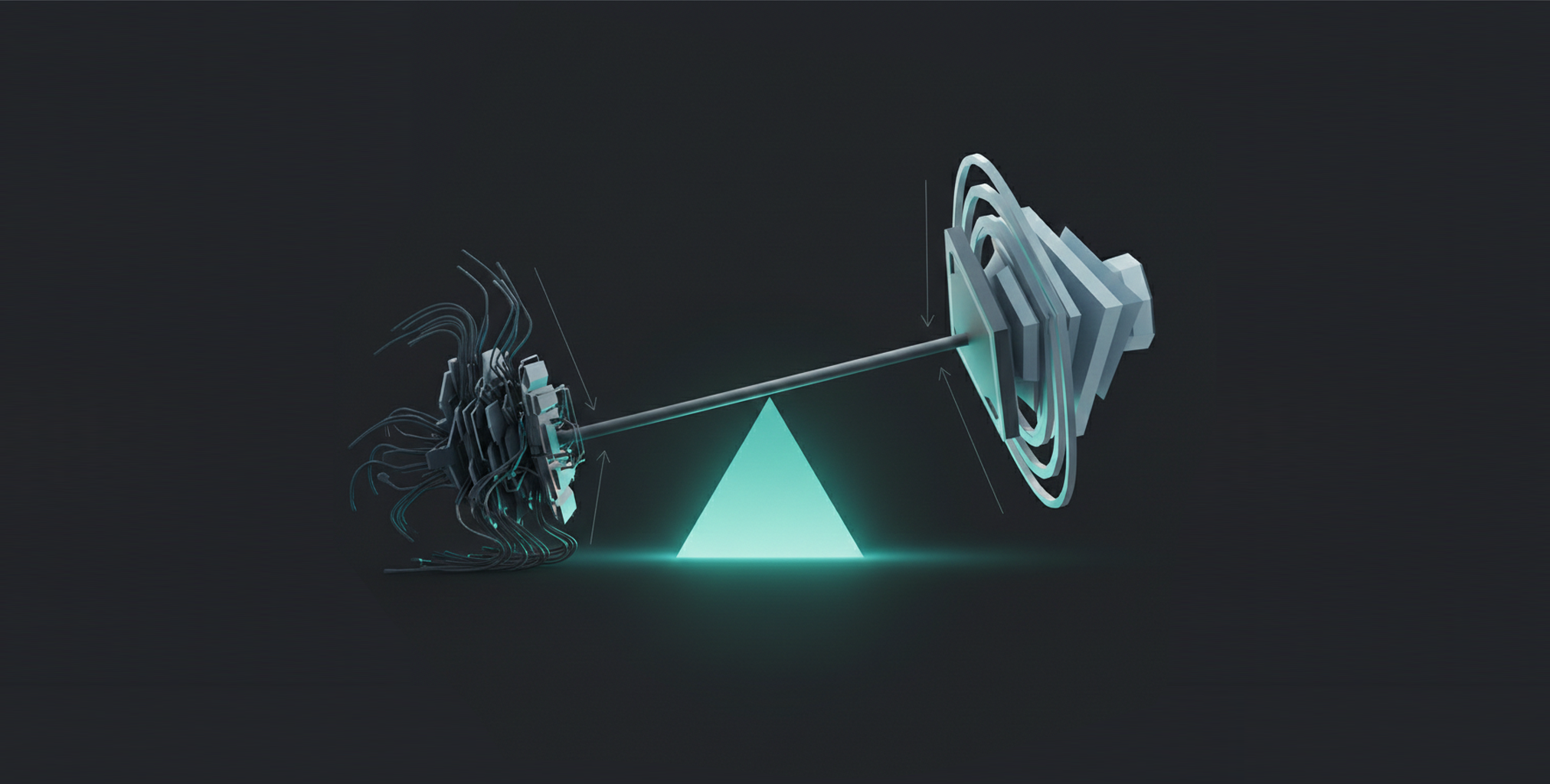
The fulcrum: the chain from pressure to harm
Pressure alone doesn't cause incidents. It needs somewhere to go.
That somewhere is vulnerability. A weakness. A gap. Something that can be exploited. …whether by a criminal or simply by circumstance.
Some vulnerabilities are technical. Unpatched systems. Misconfigured access. Weak authentication.
But many are behavioral. Reusing passwords. Skipping verification. Sharing credentials to get things done faster.
These aren't character flaws. They're rational responses to competing demands. People optimize for what the system rewards, and the system doesn't always reward security.
When pressure meets vulnerability, likelihood increases. The ‘bad thing’ becomes more probable. And the more valuable the asset(s) at risk, the greater the potential impact if it happens.
This is risk: the possibility that pressure will find a gap and cause harm.
When risk becomes reality
Most risks don't materialize. Controls hold. People make good choices. Pressure dissipates.
But sometimes, some of them do.
Risks materialize as an incident. The phishing link gets clicked. The data gets sent to the wrong recipient. The credential gets compromised.
The incident harms the asset. Data is exposed. Systems go down. Money disappears. Trust erodes.
And the incident produces outcomes, and consequences that can (and will) be measured. Financial loss. Operational disruption. Regulatory penalty. Reputational damage.
This is actual impact: not what could have happened, but what did.
The controls that stand in the way
Organizations don't just accept risk. They build defenses.
A security control environment defines what those defenses look like: policies, technologies, physical barriers, procedures.
- Administrative controls set the rules.
- Technical controls enforce them.
- Physical controls restrict access.
Together, they reduce vulnerability, lower likelihood, and limit impact.
But here's what traditional security often misses: every control depends on behavior to work.
A firewall depends on someone configuring it correctly. A policy depends on people following it. A badge system depends on people not holding the door open for strangers. Technical, administrative, physical, it doesn't matter. If the behavior doesn't happen, the control doesn't work.
Because behavior isn't one type of control. It's the foundation every control rests on.
Changing behavior, not just measuring it
If behavior is the foundation, changing behavior is the lever.
This is where behavioral intervention enters. Not training for training's sake. Not awareness posters in communal areas. Deliberate, targeted efforts to shift what people actually do.
Interventions can be triggered in three different ways:
- A corrective catalyst responds to something that went wrong.
- A directive catalyst responds to a new requirement.
- An elective catalyst responds to an opportunity to improve before anything breaks.
But whatever the trigger, effective intervention follows a disciplined path.
It starts with behaviour change techniques and evidence-based methods drawn from behavioral science.
- Prompts and cues.
- Goal setting.
- Social comparison.
- Feedback on behavior.
- Habit formation.
These are the active ingredients that make interventions work, by targeting the underlying factors that drive what people do:
Capability: Do they know how?
Opportunity: Does the environment allow it?
Motivation: Do they want to?
Change the determinants and you change the behavior. Change the behavior and you change the risk.
The loop that learns
The model doesn't end when something goes wrong. It learns.
Incidents trigger interventions. What failed? What behavior contributed? What can be changed?
Risk outcomes inform the control environment. What was the actual impact? Where were the gaps? What needs strengthening?
This creates a continuous cycle. Pressure emerges. Behavior shapes whether it succeeds. Controls mitigate what they can. Incidents happen. And the lessons feed back into better interventions and stronger defenses.
Security becomes a system that improves, not just a wall that holds or breaks.
The people at the center
This model covers threats, vulnerabilities, controls, incidents, and outcomes. It spans the full landscape of security and risk management.
But behavior is the pivot point.
Behavior contributes to vulnerability. Behavior determines whether controls work. Incidents trace back to behavioral gaps. And behavior is what interventions change.
People aren't external to the system. They're a core part of it. Their behavior materially shapes outcomes.
Recognizing this doesn't mean blaming users. It means designing systems, processes, and interventions that respect people, acknowledge the pressures they face, and make secure behavior the easy choice.
That's what human risk management is. Not catching people out. Not ticking compliance boxes. Understanding behavior well enough to change outcomes.
From theory to action
This is where SebDB comes in.
The ontology shows how the pieces connect conceptually and in practice. SebDB contains the actual data: the catalogue of security behaviors, what drives them, what changes them, and plausibility scores that assess the strength of each ‘behavior to outcome’ link.
Together, they answer the questions that matter:
Which behaviors matter most for this threat? What's preventing those behaviors? Which interventions will work?
Behavior is both the primary focus for managing human risk and the lever organizations can actually pull.
SebDB turns that insight into something you can measure and act on.
If it helps…
We’ve written the Ultimate HRM Guide for a deeper dive. It covers what HRM is, how it actually works, the behaviors that drive risk, the metrics leaders care about, and the first steps to put it to work.
And for more insights like this blog, our Behave Hub’s the place to be.
But to truly make it click, it helps to see HRM in action. You can book a demo to see how CybSafe’s human risk management platform helps teams manage risk.
I’m with you on the journey to HRM, one behavior, one outcome, one win at a time. Let’s go.

%20copy.png)





